What does Mythos mean for ASM? See here
- Platform
- Attack Surface VisibilityFrom Blind Spots to Complete Attack Surface Visibility
- Exposure ValidationIdentify, Prioritize, and Fix Critical Exposures
- Streamlined Risk WorkflowStreamline Operations to Reduce MTTR
- Active ProtectionStop Asset Takeovers Before they Become Incidents
- WAF Posture ManagementTake control of every WAF across every domain
- Solutions
- CTEM – Expose and Manage ThreatsContinuously identify, expose and remediate critical threats
- EASM – Attack Surface ManagementThe roadmap to reducing your attack surface
- CNAPP Validation – Cloud Attack SurfaceReduce Cloud Security Noise by Focusing on What Really Matters
- Control Subsidiary RiskManage cyber risk across all your subsidiaries
- Improve Security PostureReduce risk systematically
- Manage M&A riskEvaluate candidate’s cyber risk
- Threat Center
- Learn
- Company
Threat Exposure Radar ExplainedSolutions -
-
Marc GaffanApril 13, 2026
Are You Ready for the CVE Avalanche?
-
Matt MacKinnonFebruary 17, 2026
Dangling DNS in the AI Era: The Silent Attack Surface Expanding Beneath Your Feet
-
Marc GaffanFebruary 2, 2026
Deep Active Browser-Based Crawling: A Must-Have in Determining External Exposure
-
Marc GaffanJanuary 6, 2026
The Need for Speed in Exposure Validation
-
Tal ZamirDecember 25, 2025
CVE-2025-68613: Critical RCE in n8n via expression injection
-
Zach BistraNovember 26, 2025
CVE-2025-61757: Critical Pre-Auth RCE in Oracle Identity Manager
-
Zach BistraNovember 23, 2025
CVE-2025-9501: Identifying High-Risk WordPress Instances Using W3 Total Cache
-
Marc GaffanNovember 6, 2025
Why External Exposure Management Must Be at the Core of Your Security Operations
-
Marc GaffanNovember 3, 2025
Let’s be blunt, External Attack Surface Management (EASM) has run its course. It’s now all about External Exposure Management (EEM).
-
Billy HoffmanOctober 9, 2025
Exposed, Misconfigured and Forgotten: The Triple Threat of External Risk (and how to fix with Cloudflare and IONIX)
-
Tal ZamirSeptember 26, 2025
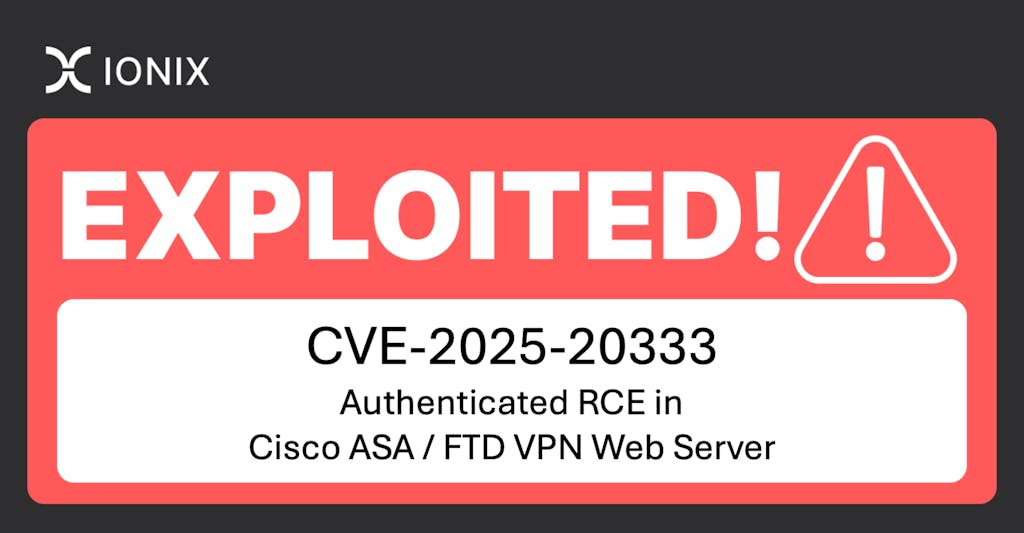
CVE-2025-20333: Authenticated RCE in Cisco ASA / FTD VPN Web Server
IONIX Cloud Exposure ValidatorProductTHE IONIX BLOG
Billy HoffmanApril 20, 2026Tired of hearing about Mythos? Your Board isn’t.
And neither are attackers. Claude Mythos Preview has been public for less than two weeks. Vendor newsletters and LinkedIn feeds have covered it to exhaustion. Meanwhile, your Board has one question, in plain language, not acronyms: what does this mean for our company and are we prepared? Mythos, in plain language Anthropic released Claude Mythos…Read moreTHE LATEST FROM IONIX >>
LATEST