Operationalizing Threat Intelligence with Attack Surface Management

Threat Intelligence is an important capability that many SOCs use to improve their security posture. Understanding what threat actors are targeting and how, can aid in everything from threat hunting to incident response. However, organizations often struggle with how to operationalize threat intelligence data they receive in order to actually accomplish this.
In this post, we will see how viewing threat intelligence through the lens of your organization’s attack surface and digital supply chain can make it more actionable. We will see how by pairing Attack Surface Management solutions with Threat Intelligence, you can increase the ROI of your security budget, while decreasing the overall risk to your organization. Finally, we will see how IONIX’s new Threat Center can help automate all of this.
The Promises and Challenges of Threat Intelligence
When I talk with organizations about how they are using threat intelligence to help improve the efficiency and capabilities of their SOC, they cite many potential benefits:
- Threat Intelligence aids in overall situation awareness. It gives the SOC news on current threat actors, their tactics, techniques, and procedures (TTPs), and systems or vulnerabilities which they may be targeting.
- Threat Intelligence aids in threat hunting. It provides a constant stream of new Indicators of Compromise (IoC) such as file hashes, domain names, and IP addresses, which the SOC searches and alerts on.
- Threat Intelligence aids in incident response.
However, when I dig into how organizations are actually using this information, I find there is often a gap between what they hope to accomplish, and what they are able to accomplish. Specifically, I see that while a lot of organizations appreciate the insights they get from threat intelligence, they struggle to operationalize those insights. Just a few examples from recent conversations:
- “Ok, I now know that Group X is targeting Y technology. So…. do we have that? If so, where?”
- “I’ve searched logs from our systems, and they don’t contain any current IoC’s like a known bad IPs or domains. But did I search all the systems that make up my attack surface? Do I have blind spots? How accurate is my view?”
- “For that matter, what about my digital supply chain? Even if all our systems aren’t at risk from what I’m hearing about from my threat intelligence feeds, what about all those 3rd party components across all our web properties?”
- “Given that these are the current active threats, how does that change my priorities for fixing systems?”
- “Ok, we had an incident, and they got in via X technology or Y vulnerability. Where else do we have that?”
This is what I mean by operationalizing threat intelligence. To use threat intelligence efficiently, organizations need to understand how that intelligence applies to them. How do you go from just knowing that a random threat actor is conducting some type of attack against certain types of assets, somewhere out on the internet, to knowing what assets you are responsible for that are likely targets for those threats?
The answer is to couple threat intelligence with a comprehensive understanding of your attack surface. Consider the figure below:
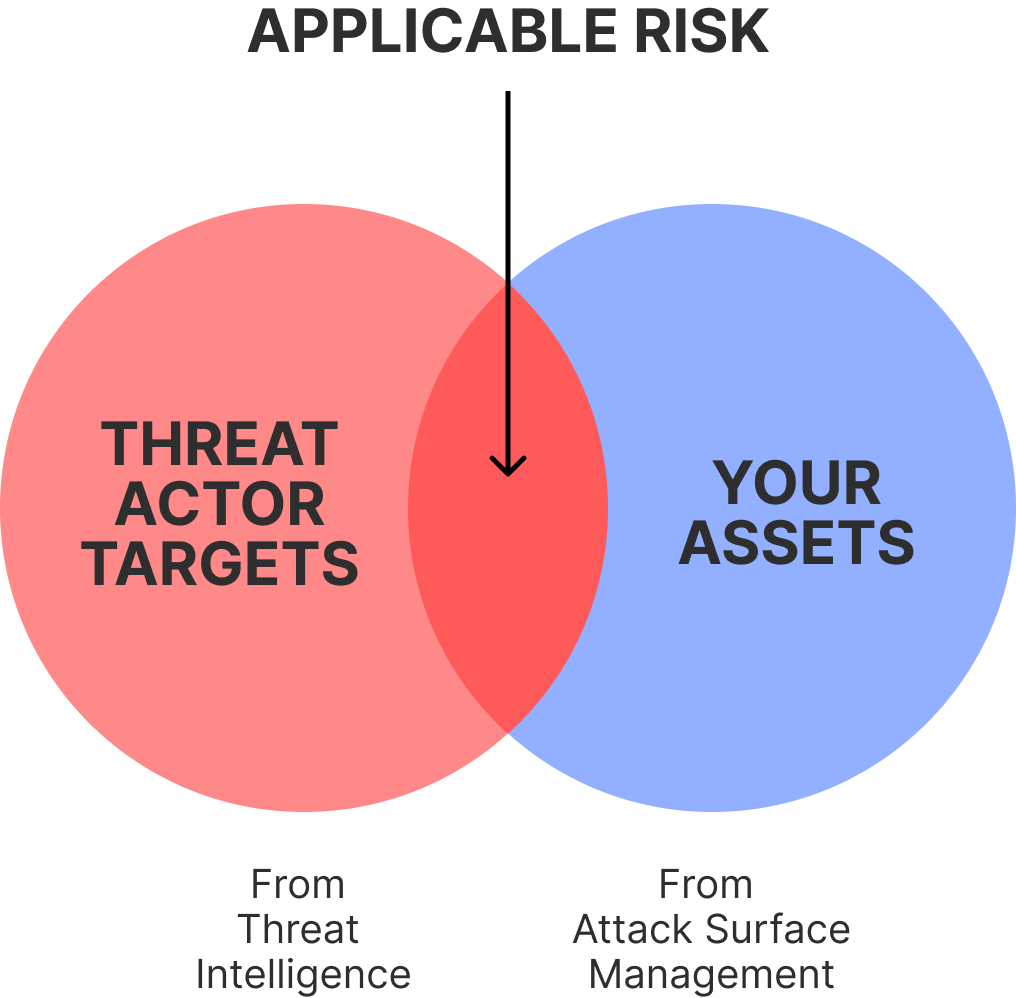
The left circle is all the attacks, threat actors, vulnerabilities, IoCs, and other things you get from a threat intelligence solution. While the entirety of that circle is academically interesting, only a subset of it is directly important right now: The part that overlaps your attack surface.
But don’t just let two overlapping circles I drew in Photoshop in 5 minutes convince you! Let’s explore 3 specific examples of how you can make threat intelligence actionable by viewing it through a lens of your attack surface and digital supply chain.
Applicability of Threats to Your Organization
Threat intelligence can tell you which groups are using specific tactics, techniques, and procedures (TTPs), targeting certain types of assets, and leveraging a specified vulnerability.
Ok, do you care? Should you care?
Attack Surface Management answers those questions and makes this information actionable by telling you if and where you have those assets, and if and where you are running services with those vulnerabilities. Attack Surface Management takes threat intelligence from the abstract (“here is what is happening somewhere on the internet”) to the concrete (“here is where I am at risk from an active group”).
Prioritization by Threat
A well- functioning SOC must be careful in how it prioritizes its work. This is because in any sufficiently sized organization, the list of things to secure is almost never-ending. Where to spend your attention and time is key.
Attack surface management tools already provide important context to prioritize hardening your discovered attack surface. Combining attack surface management with threat intelligence provides another factor in prioritization: Show me assets or vulnerable services that are actively being sought out and exploited. By combining threat intelligence with attack surface management, organizations have insights into their asset risks based on their likelihood of exploitation by threat actors.
Incident Response and Additional Entry Points
Threat Intelligence is essential when dealing with a security incident. Personally, I find using hashes of malware or RATs that have been left behind to be especially helpful. A critical part of incident response is that once you understand where and how someone got in, you need to understand the other areas of your organization that are vulnerable to the same approach. For example, where else is that vulnerable software also being used? Pairing threat intelligence with an attack surface management solution enables you to quickly check the rest of your organization’s inventory and internet facing assets for similar scenarios to the incident you are resolving.
IONIX Threat Center
Do you need to understand the impact of new threats on your organization? Do you want to operationalize threat intelligence? Then you are going to love IONIX’s new Threat Center.
The Threat Center provides customers with a list of newly announced Zero Day/One Day vulnerabilities so they can keep on top of the latest threats, all powered by the IONIX research team. Even better, IONIX Threat Center allows you to view this through the lens of what is applicable to your attack surface in the digital supply chain. Consider this figure:
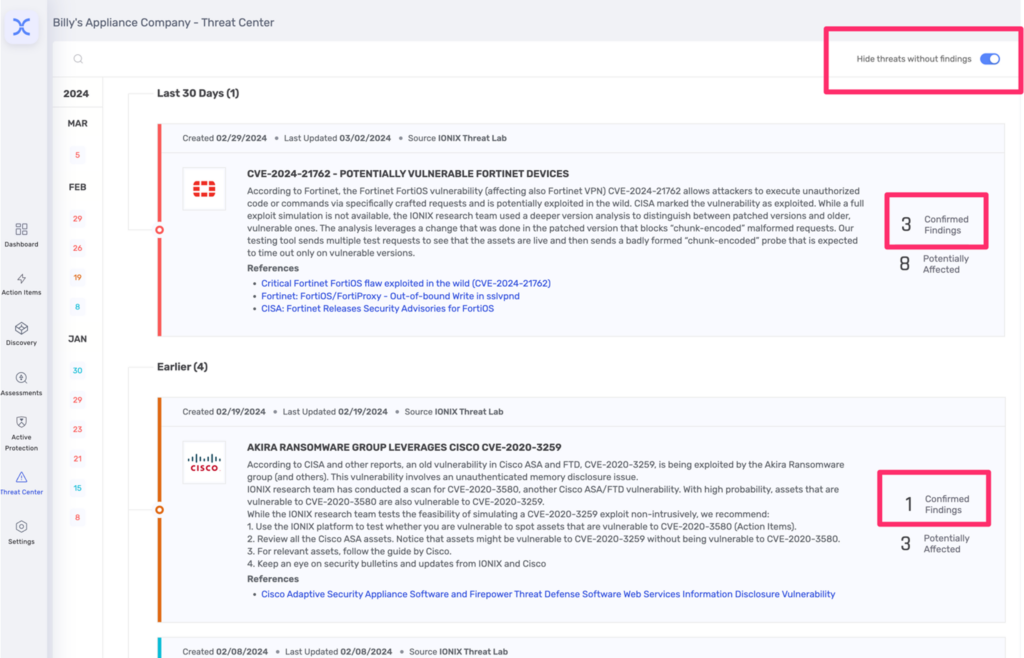
Here we see a list of Zero Day/One Day vulnerabilities that SOCs should be aware of. But it’s not just a list of vulnerabilities. It is filtered to only show you active Zero Day/One Day vulnerabilities that apply to your assets. This is shown with the “Confirmed Findings” number, showing how many assets you have which are impacted by the threat! This context takes the Threat Center from a list of abstractly interesting concerns to a list of threats you need to address!
Ready to try IONIX? Start with a Free Scan of your complete attack surface here.
Conclusions
In this post, we discussed the substantial benefits that threat intelligence can provide. We examined why organizations can struggle to operationalize the intelligence they receive. We explored three specific examples of how organizations can use an attack surface management solution like IONIX to overcome these challenges. Finally, we saw how IONIX’s new Threat Center feature helps organizations do this automatically.




