What does Mythos mean for ASM? See here
- Platform
- Solutions
- CTEM – Expose and Manage ThreatsContinuously identify, expose and remediate critical threats
- EASM – Attack Surface ManagementThe roadmap to reducing your attack surface
- CNAPP Validation – Cloud Attack SurfaceReduce Cloud Security Noise by Focusing on What Really Matters
- Control Subsidiary RiskManage cyber risk across all your subsidiaries
- Improve Security PostureReduce risk systematically
- Manage M&A riskEvaluate candidate’s cyber risk
- Threat Center
- Learn
- Company

 Threat Exposure Radar ExplainedSolutions
Threat Exposure Radar ExplainedSolutions - SLA Target: 100% of new CVEs
- SLA Target: 80% of new CVEs
- SLA Target: 80% of new CVEs

 IONIX Cloud Exposure ValidatorProduct
IONIX Cloud Exposure ValidatorProductAnthropic Mythos
The CVE Landscape Has Changed.
Here’s What It Means For You.
What Just Happened
On April 7, 2026, Anthropic published findings from Claude Mythos – an AI model that autonomously discovered thousands of zero-day vulnerabilities across every major OS, browser, and open-source project, and developed working exploits for them overnight. These were bugs that had been sitting unpatched in production environments for 10 to 27 years, found at a scale no human team could match.
Anthropic chose not to release Mythos publicly, and launched Project Glasswing – a $100M effort to help major technology companies patch these vulnerabilities before they could be exploited.
This is the beginning, not the exception. What Anthropic demonstrated responsibly today, others will attempt to deploy offensively tomorrow.
Why This Matters For Your Organization
The significance of Mythos is not the specific vulnerabilities it found. It’s what it signals about the future.
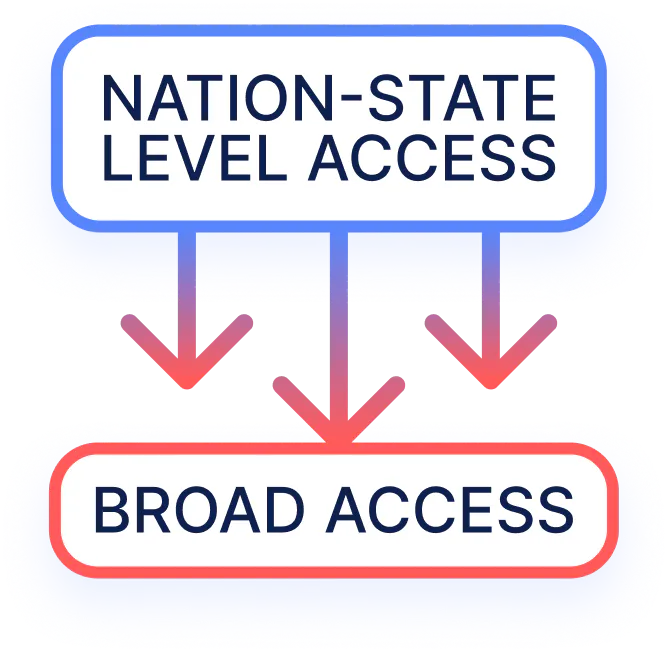
The bar for adversaries has permanently dropped.
Discovering zero-day vulnerabilities used to require nation-state-level expertise. That barrier is now eroding – capabilities once reserved for the most advanced attackers in the world are becoming more broadly accessible.
The volume is about to spike dramatically.
More AI systems will be used to discover vulnerabilities faster than the industry has ever seen. The CVE pipeline – already growing year over year – is about to experience a step-function increase. Security teams that are already stretched managing dozens of critical CVEs per month should prepare for hundreds.
The exploitation window has collapsed.
Before Mythos, the average time between CVE disclosure and active exploitation was measured in weeks. That window is now closing to hours. Traditional patch management timelines – assess, prioritize, schedule, test, deploy – were built for a world that no longer exists.
Your supply chain exposure matters more than ever.
Many of the vulnerabilities Mythos discovered are in open-source libraries and widely-used components embedded in enterprise products across the industry. Your exposure isn’t limited to software you wrote – it extends to everything running on your assets, including dependencies you may not be actively tracking.
What Your Organization Should Do
This is not a moment for panic. It is a moment for preparation.
Know your external attack surface – and the technology running on it.
You can't respond to a CVE if you don't know which of your assets are affected. Continuously updated visibility into your externally exposed assets and their full technology stack is the foundation everything else depends on.
Don't rely solely on patches – have compensating controls ready.
Patches take time: from vendors, from internal change control, from testing. Organizations need mitigations that can be deployed in minutes – WAF rules, network segmentation, configuration changes – to bridge the gap while a patch is prepared. These aren't substitutes for patching; they're the controls that protect you while you patch.
Invest in your alerting infrastructure.
In a world where exploits can appear hours after a CVE is published, being one of the first to know is a significant advantage. Daily digest emails are no longer sufficient. You need immediate, targeted alerts the moment a critical CVE is published that matches the technology running on your assets.
How IONIX Helps
Operationalizing the CVE AvalancheT+0CVE Published
Within Minutes
Threat Center Alert
Agent detects CVE publication and auto-triages against KEV, EPSS & attack surface relevance. Only externally reachable, high & critical CVEs published.
~4 Hours
Exposed Assets Identified
Agent matches CVE against technology fingerprints across your full attack surface. New fingerprints built on demand.
~8 Hours
Validate & Mitigate
Agent builds a safe, non-destructive validation payload. Once verified by a human it runs it against your assets. For each confirmed exploitable asset, a ready-to-deploy mitigation rule is generated – including WAF rules for assets behind a WAF.
Customer NotificationNew CVE Detected
Potentially Exposed Assets
Confirmed Exploitable Assets & Mitigation Steps
Your Workflow
Review Alert
Assess preliminary CVE impact using CVSS and threat intelligence. No asset-specific data yet – alert internal teams to stand by.
Assess & Prepare
Review which of your specific external assets are potentially exposed. Brief asset owners. Map existing security controls covering affected assets.
Respond & Mitigate
Know exactly which of your assets are confirmed exploitable. Deploy mitigation rules (including WAF rules where applicable). Coordinate permanent patch in parallel.
The OutcomeWithin hours of a CVE going public, you see which of your assets are truly exploitable – with a ready-to-deploy mitigation path for assets behind compensating controls.
* Agent outputs are reviewed and approved by IONIX security researchers to ensure quality and safety.
The threat landscape shifted on April 7, 2026. The organizations that respond now – with the right visibility, the right alerting, and the right response posture – are the ones that will manage this era effectively.
IONIX is here to make sure that’s you.
- Solutions