What Is the Global Attack Surface Grid (GASG)?
Gartner coined the term the Global Attack Surface Grid (GASG) to capture the evolution and increasing interconnection of an organization’s various attack surfaces. Historically, organizations have often monitored and secured IT environments in isolation with tools designed specifically for them.
In this article
However, new technologies close gaps between various attack surfaces, creating a complex and interconnected infrastructure. As a result, new technologies and security processes are required to manage the risks introduced by these interdependencies.
What Makes Up the GASG?
The GASG is Gartner’s term for the growing number of interconnected systems that might be the target of cyberattacks. Key elements of the GASG include:
- Traditional IT Systems: Traditional IT systems include those devices, applications, and other entities traditionally secured by corporate cybersecurity programs. This includes servers, workstations, applications, databases, and more.
- Cyber-Physical Systems: Cyber-physical systems bridge the gap between the digital and physical spaces. Internet of Things (IoT) devices are a prime example, especially in spaces like manufacturing, transportation, and healthcare, where Internet-connected devices can have direct impacts on the physical world.
- Electromagnetic Spectrum: Modern businesses are increasingly reliant on various bands of the electromagnetic spectrum for communications. Wi-Fi, mobile networks, near-field communications (NFC), and the radios used by police and first responders all rely on electromagnetic signals that might be jammed or corrupted by an attacker.
- Space Infrastructure: Growing interest in satellites, space stations, and spacecraft introduces a new realm of systems and threats. Space systems must be secured against potential attack and require reliable, secure connectivity with terrestrial systems as well.
- Security Earth Intelligence: Security Earth intelligence includes the use of geospatial intelligence (GEOINT) and Earth observation (EO) data to enhance security. Data collected from space can be analyzed by AI and used to enhance physical security.
- Autonomous Systems: The growth of artificial intelligence (AI) has introduced new attack surfaces, especially as agentic AI allows these systems to work autonomously. Prompt injection, corrupted training data, and similar attacks can impact the effectiveness and trustworthiness of these systems.
- Agentic Identities: Agentic AI systems commonly have widespread access to corporate data and systems to perform their roles. Traditional identity and access management (IAM) is ill-suited to managing the risks associated with this access, requiring more tailored, scalable, and adaptable identity management solutions.
Major Trends in the GASG
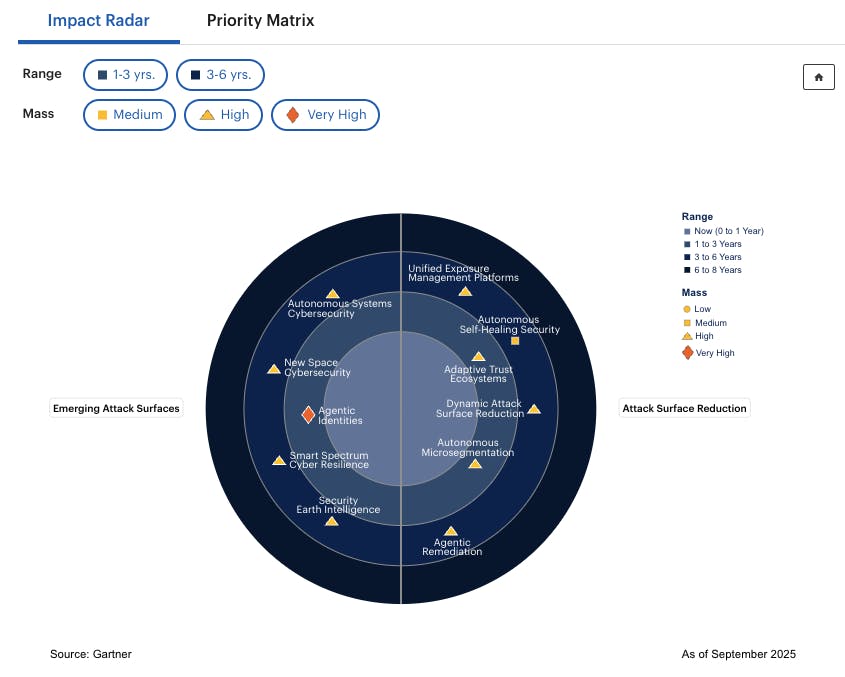
When defining the GASG, Gartner identified several trends that will shape organizations’ security programs and that mandate the use of tools like Dynamic Attack Surface Reduction (DASR). These include:
- Emerging Attack Surfaces: Many elements of the GASG include technologies that are in their infancy, such as space technology and autonomous systems. These will introduce new, unpredictable risks that corporate security architectures will need to prepare for and address in the future.
- Growing Interconnectivity: Historically, various elements of an organization’s security program, such as IT and physical security, were largely distinct. However, the introduction of cyber-physical systems and other new technologies closes these gaps and requires a more comprehensive approach to cybersecurity and threat management.
- Proactive Defense: The combination of new attack surfaces and growing interconnectivity means that traditional, reactive approaches to security are no longer effective. DASR is one element of a proactive security strategy designed to close security gaps and block attacks before they happen rather than scrambling to respond to an in-progress attack.
Managing the Evolving GASG
Gartner coined the term GASG to highlight the fact that organizations’ threat exposure and attack surfaces are changing in a way that requires a complete overhaul of traditional security programs. In the near future, companies will be managing massive, interconnected attack surfaces that are targeted by automated, intelligent cyberattacks.
To align with corporate risk appetites and regulatory requirements, organizations will need to be proactive about security, finding and fixing potential vulnerabilities before attackers can exploit them. Accomplishing this at scale without introducing friction to legitimate business workflows requires taking advantage of automation and AI to reduce reliance on manual security workflows.
The IONIX platform is recognized by Gartner as a sample vendor in the Dynamic Attack Surface Reduction (DASR) space for its external attack surface management (EASM) capabilities. To learn how IONIX can help defend your organization against modern and future cyber threats, book a free demo.



